Microsoft recently disclosed the resolution of a critical security flaw in Power Platform, a popular tool for custom connectors. The vulnerability had the potential to allow unauthorized access to Custom Code functions, potentially leading to unintended information disclosure if sensitive data was embedded within these functions.
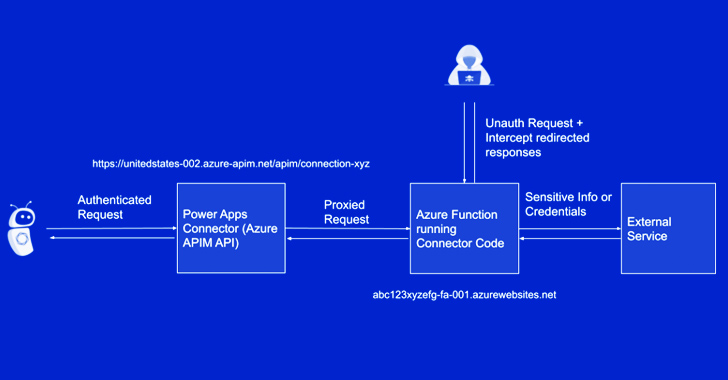
Tenable, a cybersecurity firm, first reported the flaw to Microsoft on March 30, 2023, highlighting the risk of limited, unauthorized access to cross-tenant applications and sensitive data. The vulnerability stemmed from insufficient access control to Azure Function hosts, which could enable a threat actor to intercept OAuth client IDs, secrets, and other authentication information.
Although Microsoft issued an initial fix on June 7, 2023, the flaw remained unaddressed until August 2, 2023, raising concerns and criticism from the cybersecurity community. Tenable CEO Amit Yoran accused Microsoft of being grossly irresponsible and negligent in its handling of the issue.
Yoran argued that cloud providers should adhere to the shared responsibility model, which requires timely notification and transparent fixes for security issues. However, he criticized Microsoft for lacking transparency and adopting a culture of obfuscation.
In response, Microsoft defended its security update process, claiming it carefully balances speed and safety while developing fixes. The company acknowledged that not all fixes are equal, and the complexity of vulnerabilities may affect the time required for resolution.
Microsoft assured that it monitors reported security vulnerabilities actively and responds swiftly to any active exploits to protect its customers. Despite the criticism, the tech giant emphasized its commitment to safeguarding its users and providing a secure environment.
Đăng ký liền tay Nhận Ngay Bài Mới
Subscribe ngay
Cám ơn bạn đã đăng ký !
Lỗi đăng ký !











Add Comment