Cybercriminals have been utilizing known vulnerabilities in Microsoft Word documents as part of phishing attacks to distribute LokiBot malware on compromised systems.
LokiBot, also known as Loki PWS, has been an established information-stealing Trojan since 2015, primarily targeting Windows systems to gather sensitive information from infected machines, according to Fortinet FortiGuard Labs researcher Cara Lin.
The recent campaign, identified by Fortinet in May 2023, leverages CVE-2021-40444 and CVE-2022-30190 (aka Follina) to achieve code execution.

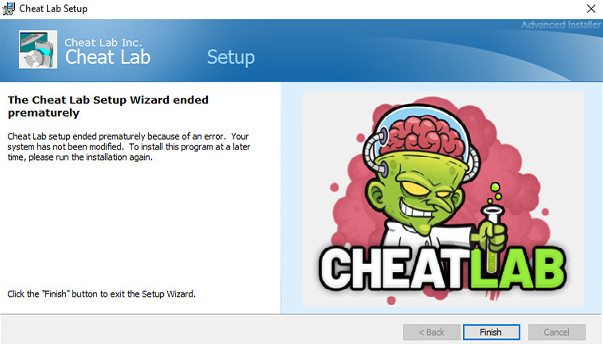
In the case of CVE-2021-40444, the Word document contains an embedded external GoFile link within an XML file. This link directs the victim to download an HTML file that exploits Follina to obtain a next-stage payload—an injector module written in Visual Basic. This injector module decrypts and initiates the execution of LokiBot.
The injector module also employs evasion techniques to detect debuggers and identify whether it is running in a virtualized environment.
Another variant observed in late May involves a Word document with a VBA script that triggers a macro upon opening. The macro serves as a conduit to deliver an interim payload from a remote server, acting as an injector to load LokiBot and establish a connection to a command-and-control (C2) server.
LokiBot, unrelated to an Android banking trojan with the same name, possesses various capabilities such as keystroke logging, screenshot capture, harvesting login credentials from web browsers, and extracting data from cryptocurrency wallets.
“LokiBot is a well-established and widespread malware that has been active for many years,” explained Lin. “Its features have evolved over time, allowing cybercriminals to easily exploit it for stealing sensitive data from victims. The attackers behind LokiBot continually update their initial access methods, enabling their malware campaign to spread more efficiently and infect systems.”
Đăng ký liền tay Nhận Ngay Bài Mới
Subscribe ngay
Cám ơn bạn đã đăng ký !
Lỗi đăng ký !











Add Comment